Insightful powerful Convenient
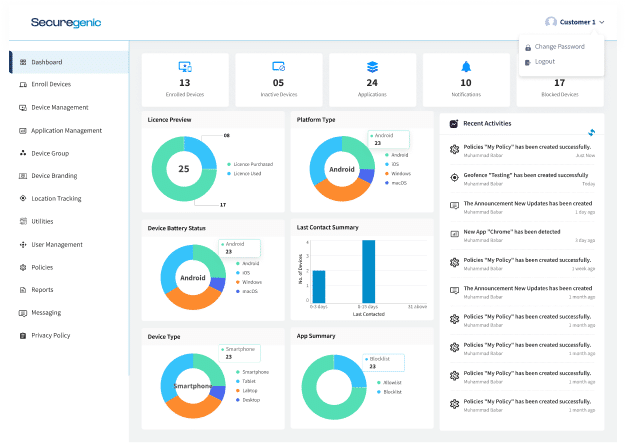
We are a 360 MDM solution that facilitates management and supports business flexibility. We assist enterprises in UAE & USA in accelerating their work and giving them total Access to over the devices. Protect corporate workstations and PCs, the majority of enterprises put a lot of effort and money to protect their mobile devices, because these devices are used for processing and storing sensitive data. Securegenic Mobile Device Management software solution provides a number of features that make it simple and affordable for you to maintain security and compliance across all of your mobile devices.
MDM Solution & Features to secure corporate workstations

Mobile device management software has a Feature called Geo-fencing that allows administrators to set up virtual boundaries or "fences" around specific geographic locations. When a device enters or exits a fenced area, it triggers a response from the MDM system, such as sending an alert to the administrator or initiating a set of automated actions on the device, such as locking or wiping the device. Tracking feature of MDM Software allows administrators to track the physical location of devices in real-time.

Allows the administrator to keep an eye on key device features including storage, data, and the battery. Keep an eye on the device, allow your employee to work remotely, and let BYOD secure your company's data when they are working from home. Additionally, device monitoring can help administrators identify potential security threats and take proactive steps to mitigate them. Enterprise mobile device management system has to be secure from all the security threats, BYOD policies allow employees to use their own devices for work.

One of the key features of enterprise mobile device management solution is the ability to remotely wipe data from lost or stolen devices. This is very important for protecting sensitive corporate data and preventing it from falling into the wrong hands. With mobile device management software, administrators can initiate a remote wipe of a device, erasing all data and settings. MDM Software with this special Remote wipe features has ensures the security when your device is lost.

With the Help of this Securegenic MDM solution admin can easily access all the reports of device which includes account Activities, usage of the data, Location, applications that user has downloaded, files that are sent and received, file docs analytics and Remote cast. Mobile device management includes MDM reporting, which is essential. You are unable to monitor the success and progress of your mobile device deployment without it.
Securegenic offer centralized management and security for mobile devices, including features such as device enrollment, application management, and remote wipe capabilities.
Our experts will offer you free guidance and support, as well as assist you in real-time problem-solving for administration and monitoring concerns regarding securing and managing mobile devices. If you have any questions or concerns about device management solutions, connect with us right away.
At our company, we understand that every business has unique device management needs, and that's why we offer tailored solutions to meet those needs. Our team of experts will work with you to understand your specific requirements and recommend a device management solution that's best suited for your business.

Our MDM software supports your Device’s Security and provides protection against malware sites and other security threats. Securing and managing mobile devices & Protect the data from Breaches is what MDM Solution is for. Don't take risk with the security of your devices. – Contact us today to learn more about our enterprise mobile management solutions.
Solutions for a Modern Workforce
Complete Access to your Corporate Devices

The management of a fleet of devices requires careful attention to device monitoring, particularly when BYOD (Bring Your Own Device) policies are in effect. Administrators can make sure that staff are not encountering any problems that might reduce their productivity by keeping an eye on device features like battery, data usage, and storage. BYOD also helps in monitoring the timeline of keeping check on work.

MDM helps in Securing and managing mobile devices, this Feature Prevent Users from sharing the data from working email and apps to personal apps. Preventing screen shots with MDM (Mobile Device Management) is a useful security measure for businesses that need to protect sensitive information on mobile devices used by employees. Screen shots can capture confidential data such as passwords, personal data, financial information, and proprietary business data. Stay Secure with easy Management.
Preventing users from sharing company data from work email and apps to personal apps is essential for maintaining the security and confidentiality of sensitive business information. Without proper controls in place, employees may inadvertently or intentionally share confidential data, leading to data breaches, loss of intellectual property, and legal and regulatory compliance issues. Restriction can be implemented on android device management, iOS, macOS and windows.
The Unified Endpoint Management (UEM) system is a comprehensive approach to managing an organization's devices, including desktops, laptops, mobile phones, and tablets. It provides a single platform for managing all endpoints, allowing administrators to streamline deployment, tracking, upgrades, and security. The Unified Endpoint Management system encompasses an organization’s device and provides immediate assistance for deployment, tracking, upgrades, and security.
if you have any query regarding android device management, iOS, MacOS, or windows we at Securegenic, provides management Solution for all. we thrive to provide better services each day. Our help is available around-the-clock.
At Securegenic, we understand the importance of managing devices in an enterprise setting. That's why we provide an MDM solution that has been trusted by businesses across the globe. Our MDM software is designed to help enterprises manage their devices more effectively and securely. With our Mobile management solution, businesses can remotely manage their devices, enforce security policies. With our user-friendly interface and thorough reporting tools, organizations can effortlessly manage Their Devices and guarantee that their devices are safe and complies with corporate regulations.
Contact Sales
© 1999-2022 Securegenic . All rights reserved.